In the vast majority of UWM deployments, the default security settings are rarely changed beyond adding a single, global administrative group. This is usually because there is only a small core team managing the product, so sandboxing peoples’ capabilities is not usually required.
However maybe there is a contractor assisting with a larger effort. Or maybe a junior admin doing very targeted testing. In these instances, you may want to grant access to only update a specific policy, assigned to a specific deployment group.
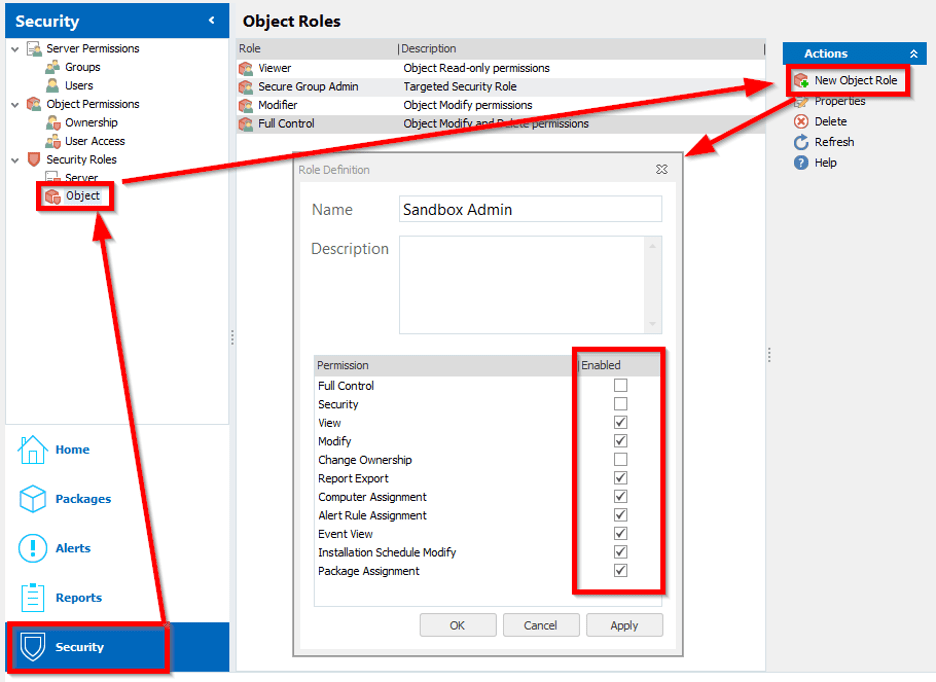
To start with this process, we need to create an “Object” Security Roll as follows:
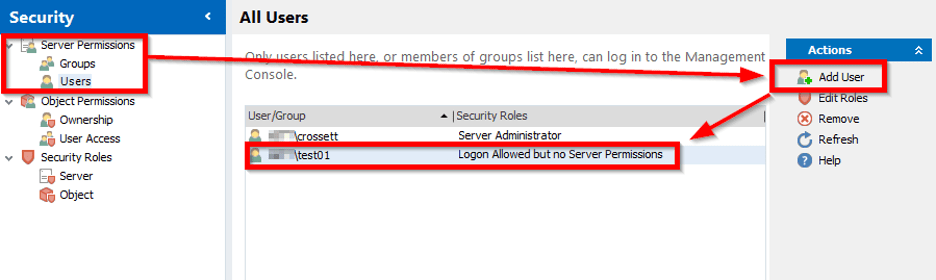
After the Object Security Roll has been created, we need to add the AD Security Group (Or user, in this example) with Logon Only permissions:
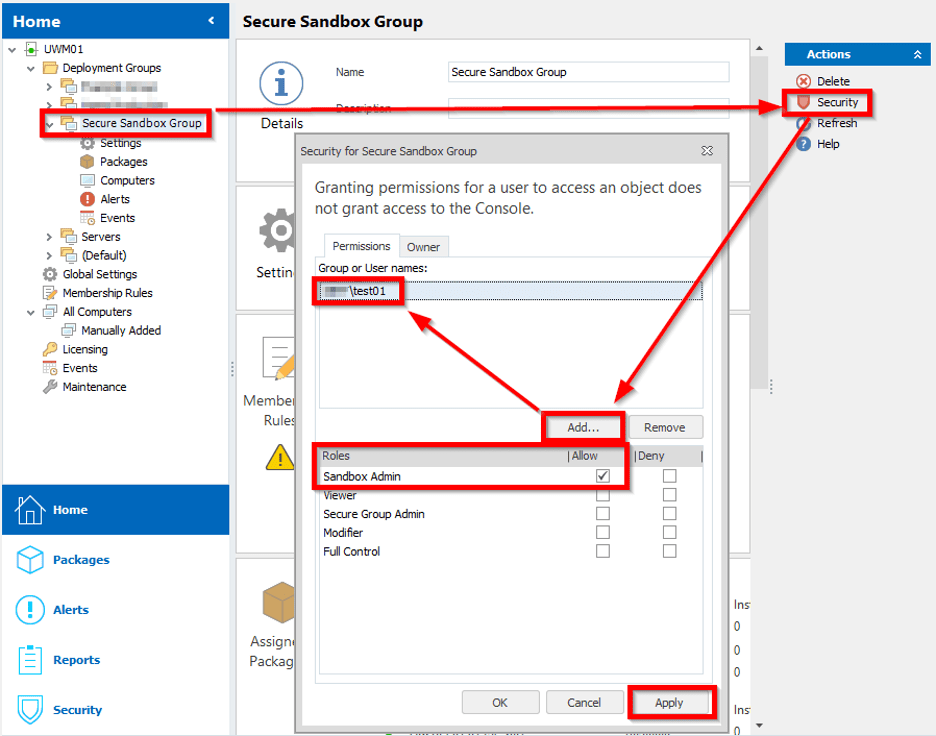
Now here is where things get a bit confusing. Instead of continuing in the Security section of the console, we have to go to the actual objects (Deployment Group and Packages) that we want to set permissions on.
In this example, we’re creating a new Deployment Group specifically for this effort called “Secure Sandbox Group”. Once that’s created, select the deployment group and go to the Security option on the right. Add the User or Group that is to be granted permission, and assign it he “Sandbox Admin” role:
At this point, our test user (or group) now has administrative access to the Secure Sandbox Group. However, they have no access to any packages to assign. To do that, we need to grant the same Role to our target user/group, on the specific package they need to be able to open, modify, save and assign.
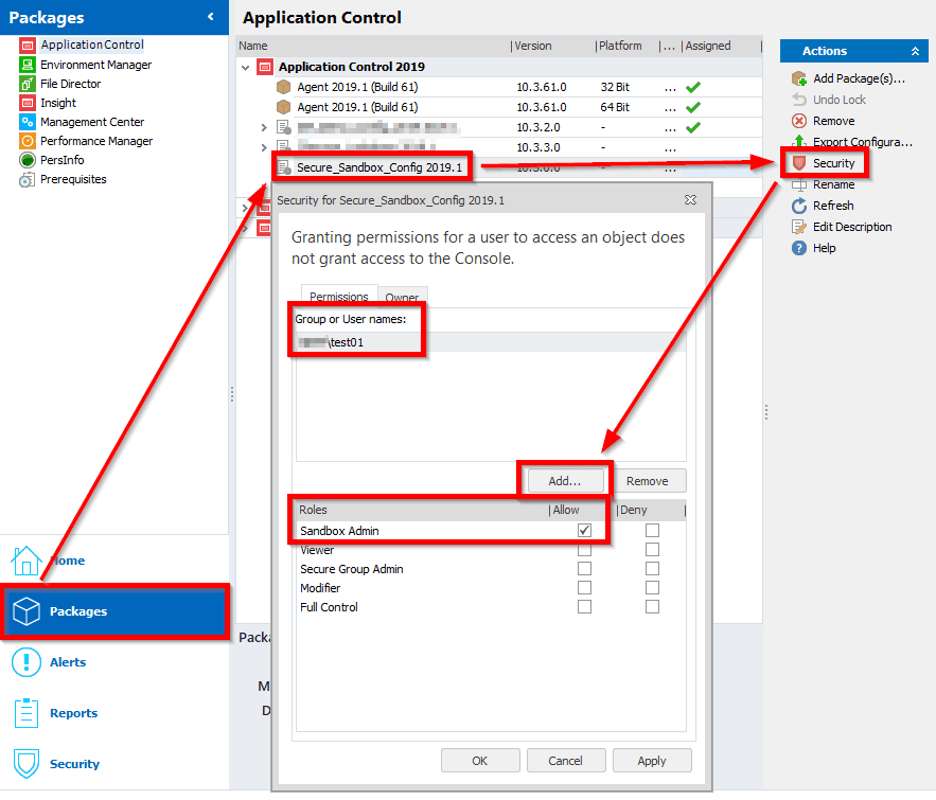
This is done from the Packages section of the console, in the Security section of our target policy:
As things sit, our sandbox user/group has the access they need to open, modify, save and assign a specific policy package to a specific security group. However, we have not (and don’t intend to) granted them rights to assign other packages to that group – like agents. Because of that, as our global admin, we’ll need to assign the base agents to the deployment group in question:
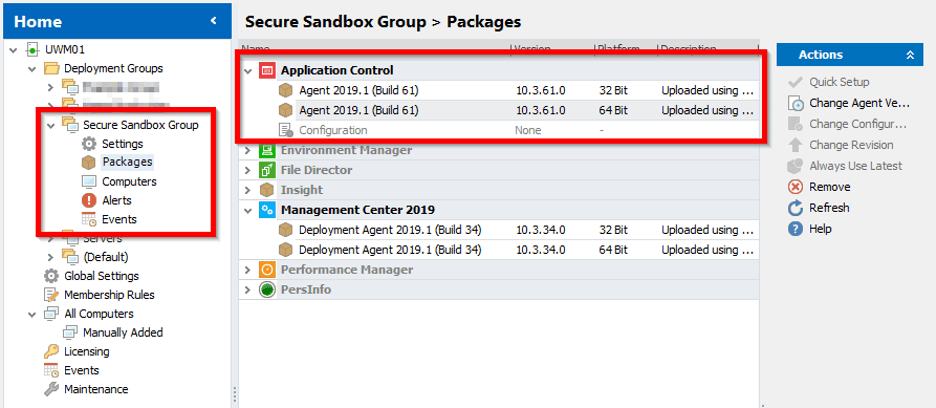
You’ll notice in this example, we’re only deploying Application Control, and we are not assigning a policy. That can be done later by our sandbox’d administrator. The targeted machines for the Sandbox group will also need to be moved ahead of time by a global administrator, as we’ve chosen not to grand our sandbox admin rights to perform this function.
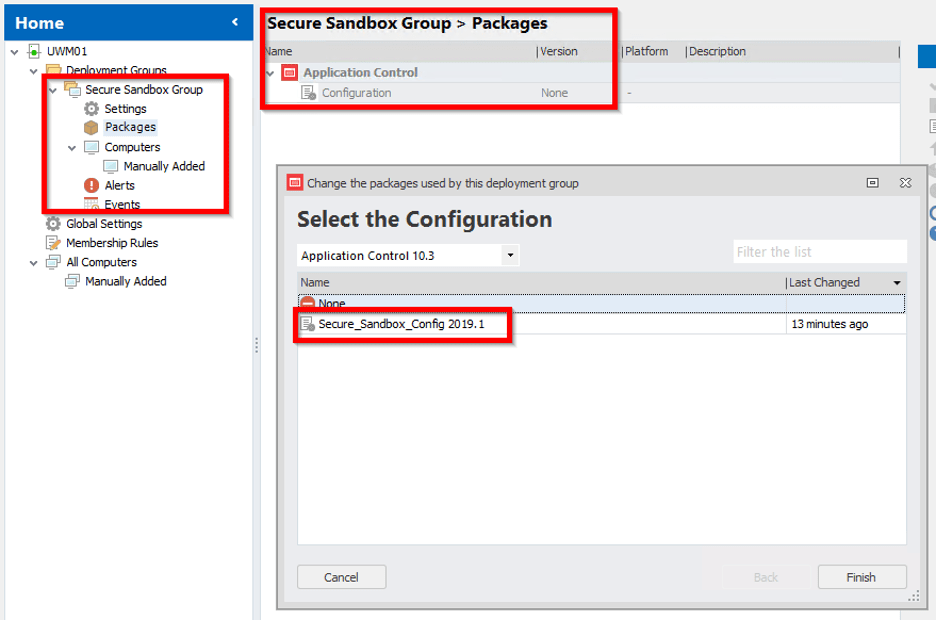
From here, we can test the process by logging into the management console as a Sandbox’d admin and see that we can only see one deployment group, and only have access to assign one package:
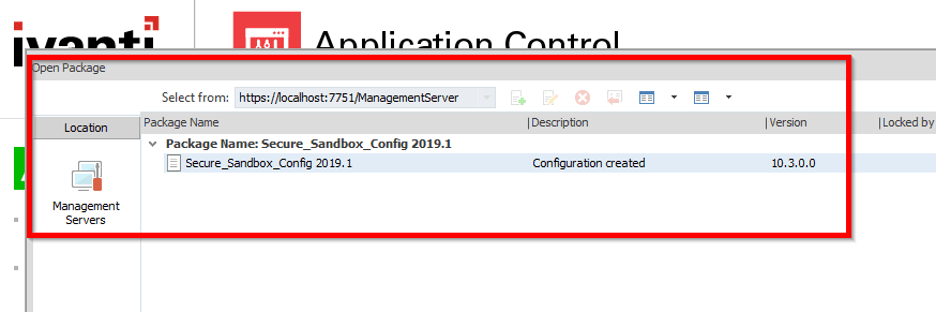
Finally, if we open up the Application Control console and connect to the Management Server as our Sandbox’d admin, we only have the ability to see and check out one policy object:
The above configuration can of course be modified to fit your organization group/user requirements but should ultimately result in a user/group than can only administer a very narrow cross section of your UWM infrastructure.
If you’d like to speak to an Ivanti expert, please don’t hesitate to reach out.