You bought it – you installed it – but are they using it? Make sure by adding the dimension of ‘utilization’ to your software reporting data, and avoid wasting another dollar on unnecessary software purchases.
Alchemy Gold
Asset Management for Modern IT
Our technology provides deep insight into your on-premise and hybrid cloud infrastructure. With real-time data, we provide actionable strategies that accelerate cloud adoption, reduce risk, and save money.
What you can expect
Our discovery platform can be optimized for even the largest and most complex networks ensuring a complete and accurate inventory of all IT assets regardless of device type, location or operating system.
Once deployed, your asset inventory is encrypted and securely transferred to a regionally located tier-4 datacenter where it is cleansed, categorized, matched and analyzed for advanced reporting; including installed software categorization, license assignment, hardware warranty matching, end-of-support/end-of-life status and cross-referenced with all known security vulnerabilities.
- Agentless discovery technology
- Fast and easy deployment
- Full hardware and software inventory
- Capacity and utilization metering
- Full public cloud connectivity
- API Based integrations
Features built for modern IT asset management professionals
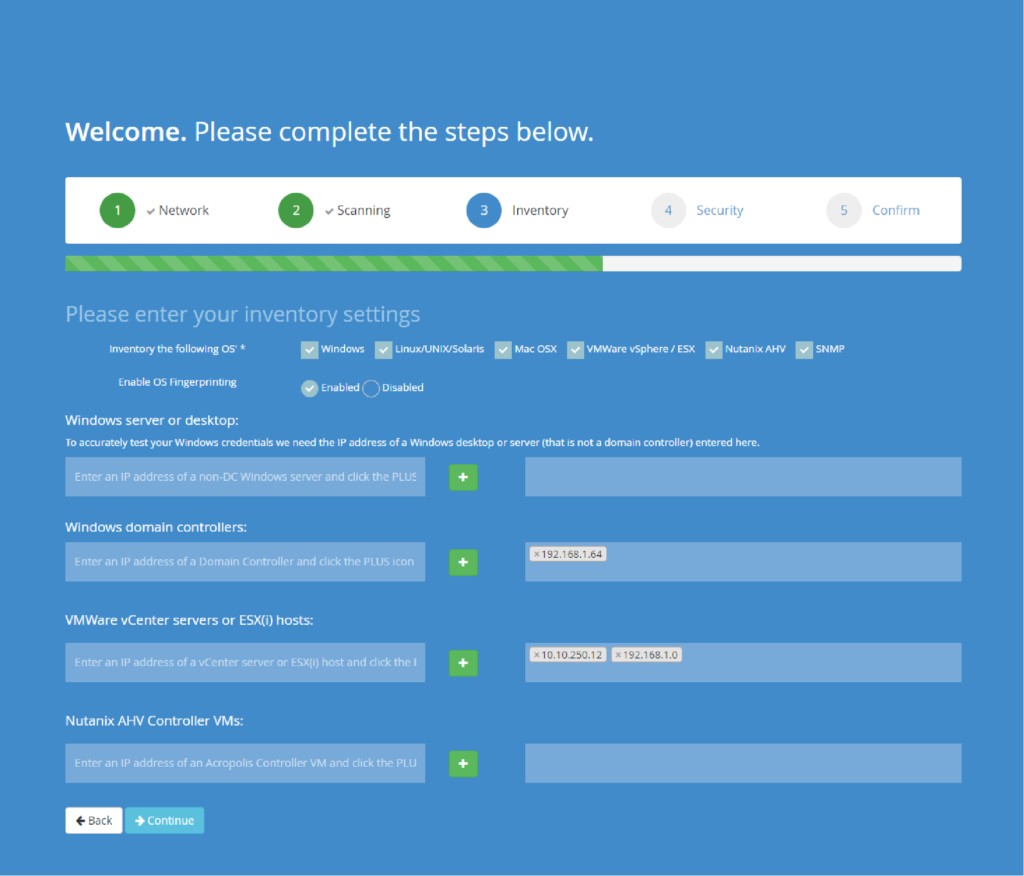
Deploy in Minutes
Any transformative IT project needs to start with a solid understanding of your current state. Our configuration wizard will guide you through installation and provide flexible options to help optimize the data collection process. Once setup, incremental discovery will continuously run ensuring a timely and thorough asset inventory without manual intervention.
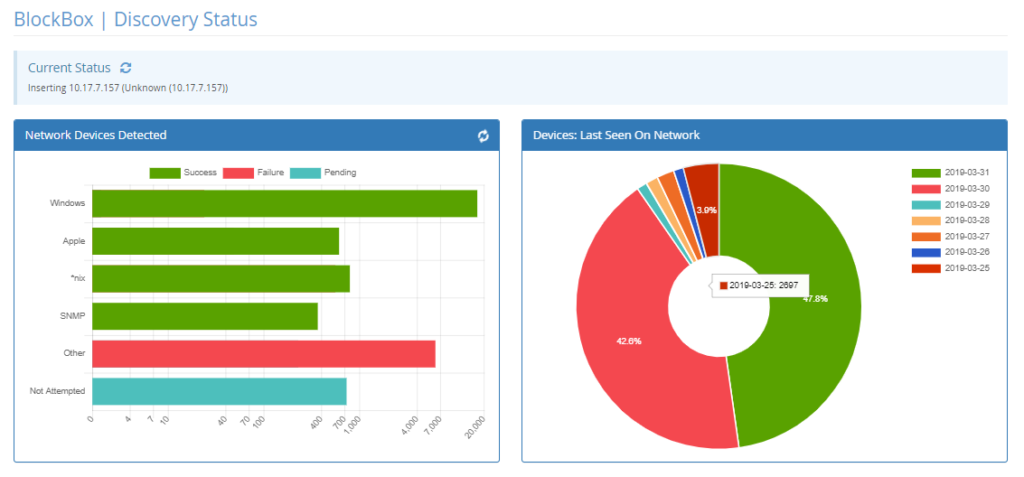
Comprehensive Asset Discovery
Our 3-step discovery method identifies assets as they connect to the network, identifies the asset type and operating system before accessing, inventorying and monitoring the device be it physical, virtual, on-premise or in the cloud. Your asset inventory will always be current with user specified re-inventory schedule that updates incrementally and continuously. Through integration with Active Directory, you will always have real-time visibility into the completeness of your inventory and more importantly, what assets may be missing.
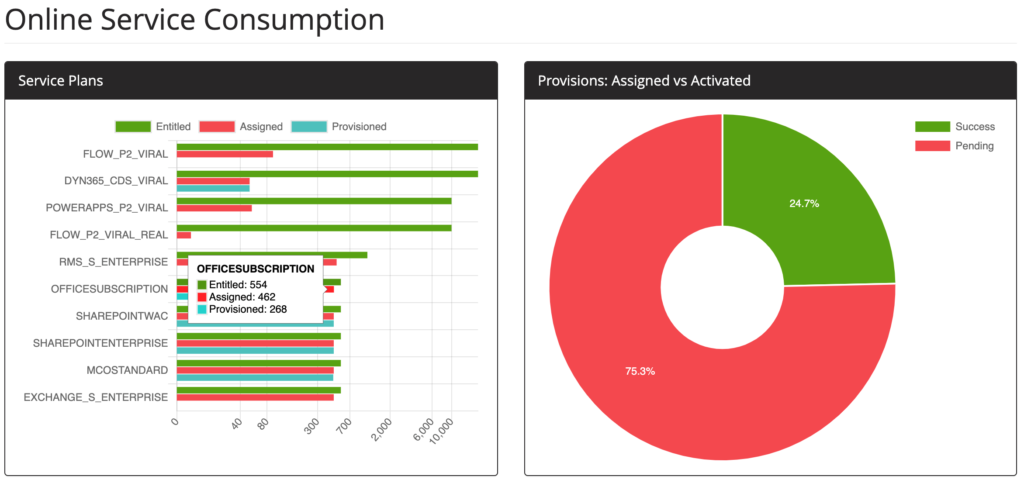
Usage Reporting and Software Metering
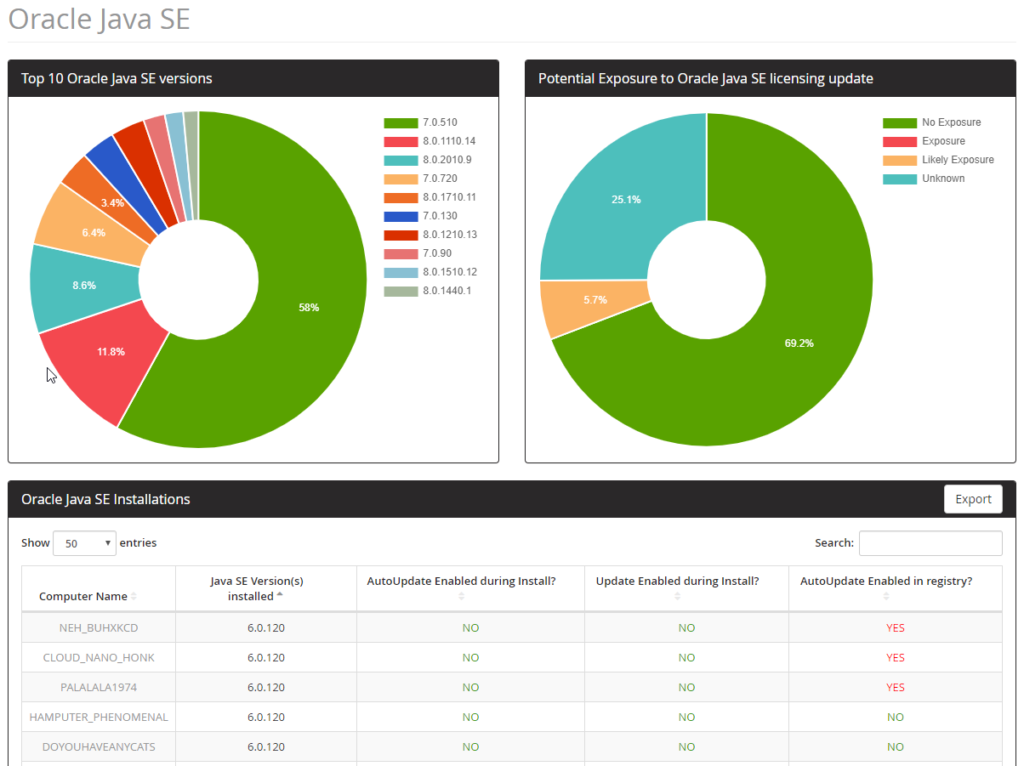
The Latest Licensing Intelligence
Licensing terms change fast and falling behind can have real-world financial implications. Our team of analysts continuously monitor changes to licensing models and product use rights to help our customers easily assess the impact on their organization. Concerned about recent news from Microsoft, Oracle (Java), Micro Focus, Quest or HPE? We got you covered.
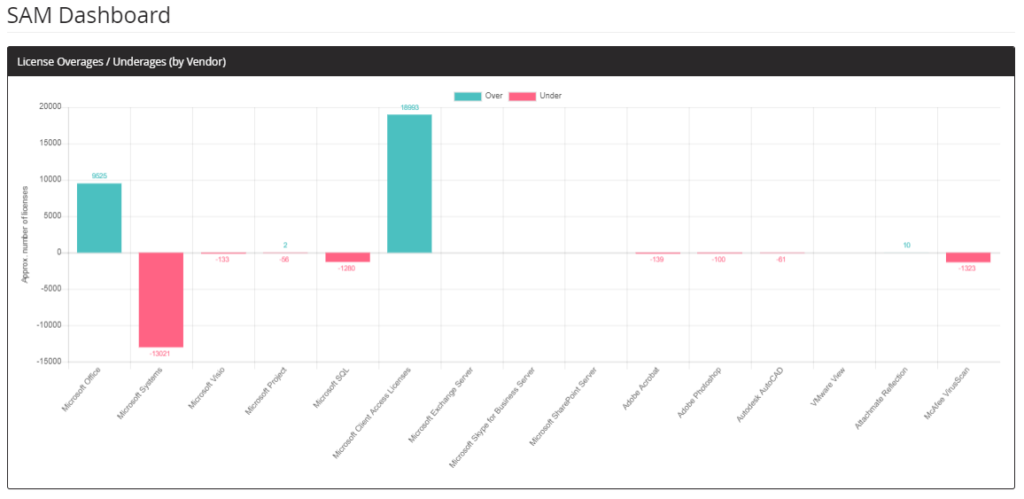
Advanced SAM Dashboards
You want to know more than just what titles you have installed – you want to know if you’re compliant. Automated gap analysis doesn’t get easier than this. Simply key your contracts and entitlement information and let the system do the rest, for the duration of the license agreement. Gain the confidence you need for critical license verification and audit defense activities.
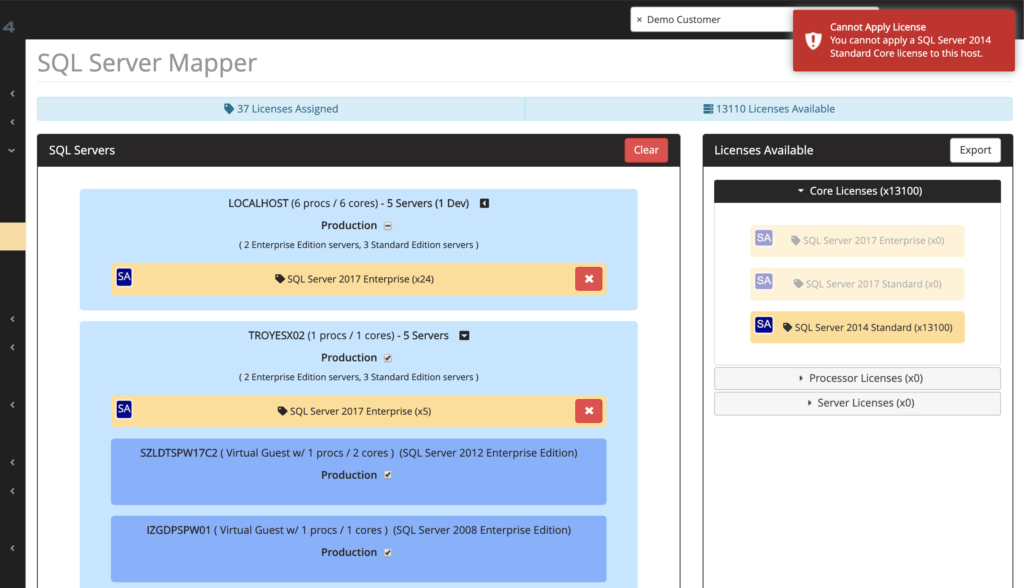
Simple and Intelligent Licensing Tools
Software licensing isn’t getting easier, and the rate of change is increasing. Diverse licensing metrics and arcane terms and conditions can make it hard to simply know if you’re ok – or in trouble. In cases where more than simple math is required, our license mapping tools will automatically assign licenses to maximize your licensing investment, while allowing for manual override when necessary, and alerting the user of incorrect license assignments.
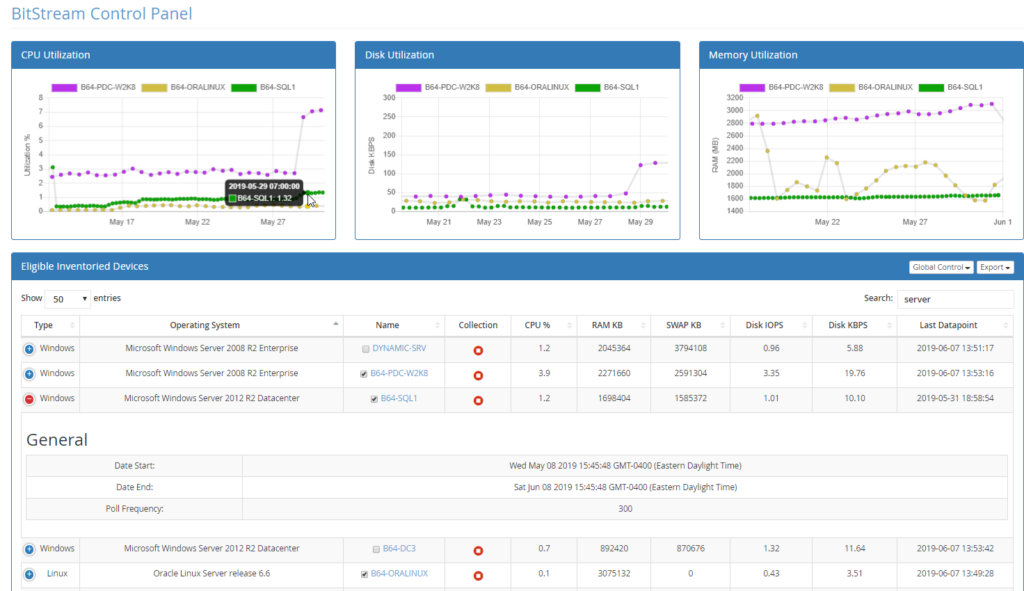
Resource Consumption and Performance Data
Leveraging over 60 different counters and datapoints, we can visualize the current utilization rates of both virtual and physical assets – across all major platforms. Our data can assist in optimizing your current environment, planning for a cloud migration, or even finetuning an application for performance.
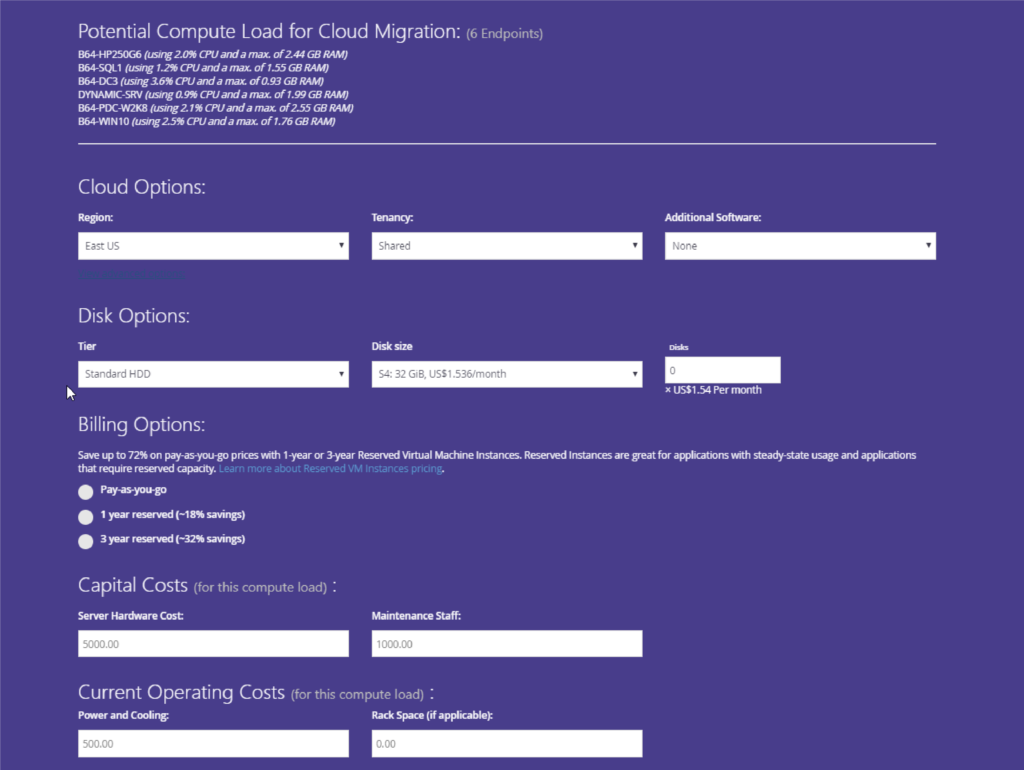
Cloud Migration Scenario Builder
Quickly model your current workloads in cloud solutions such as Azure and AWS. Our solution combines real-time pricing and sizing data and utilization readings gathered from your unique environment to model out the true cost of cloud adoption.
Hardware Lifecycle Tracking
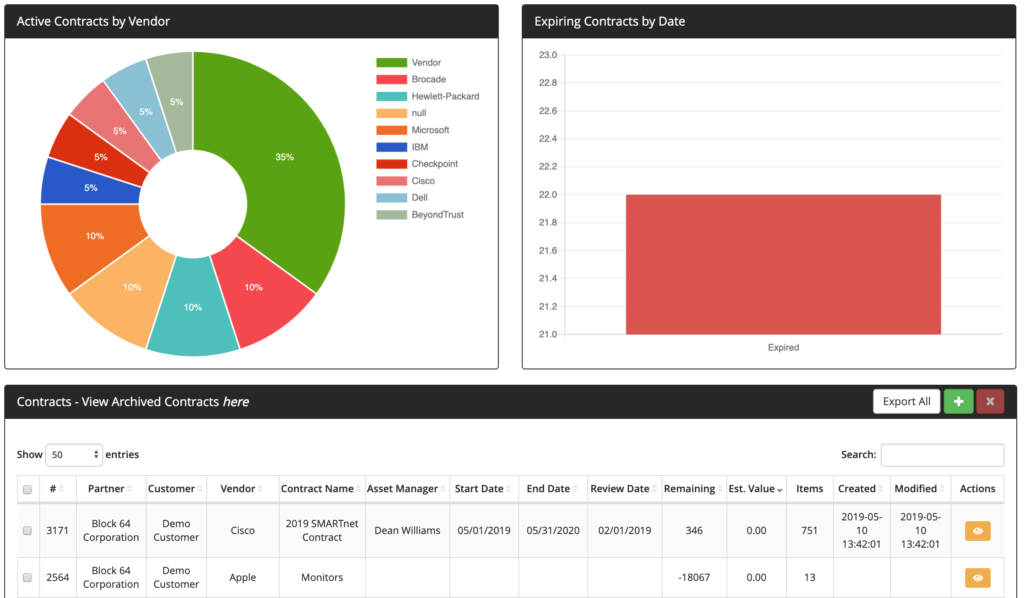
Understanding the coverage and lifecycle status of a diverse, multi-vendor IT estate can be a time-consuming task. For most major manufacturers, we can automatically pull in any maintenance, care packs or warranties tied to your fleet, with no manual intervention required.
Flexible Asset Metadata System
Not everything that can be scanned matters, and not everything that matters can be scanned. Our asset metadata system allows you to affix key asset data such as financial, procurement, contractual, and location data to your asset repository – allowing you to have the key data needed for IT decision-making on hand and all in one place.
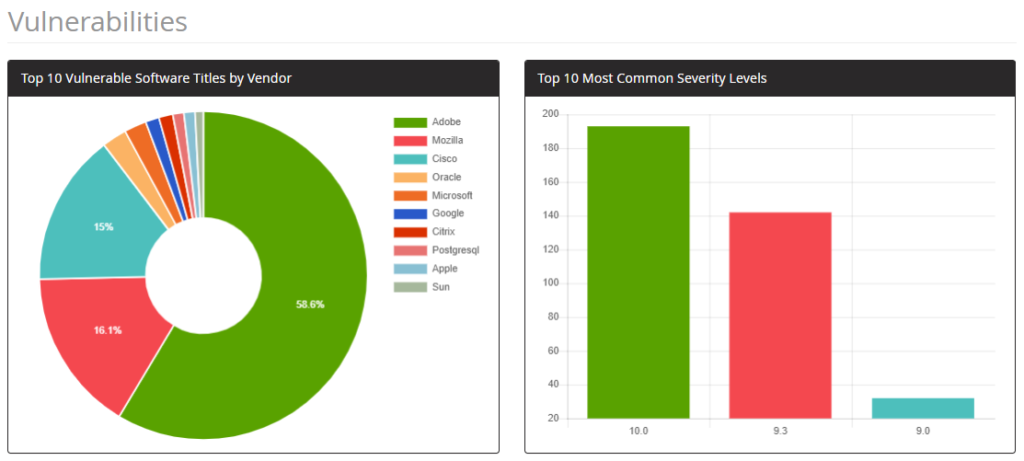
Vulnerability and Threat Reporting
Monitor current threats and uncover exposure points for proactive remediation. Our vulnerability repository will highlight any unpatched titles or configurations in your mixed environment. Stay on top of end-of-support and end-of-life software and hardware in your environment and remove legacy technology before it presents a risk to your organization.
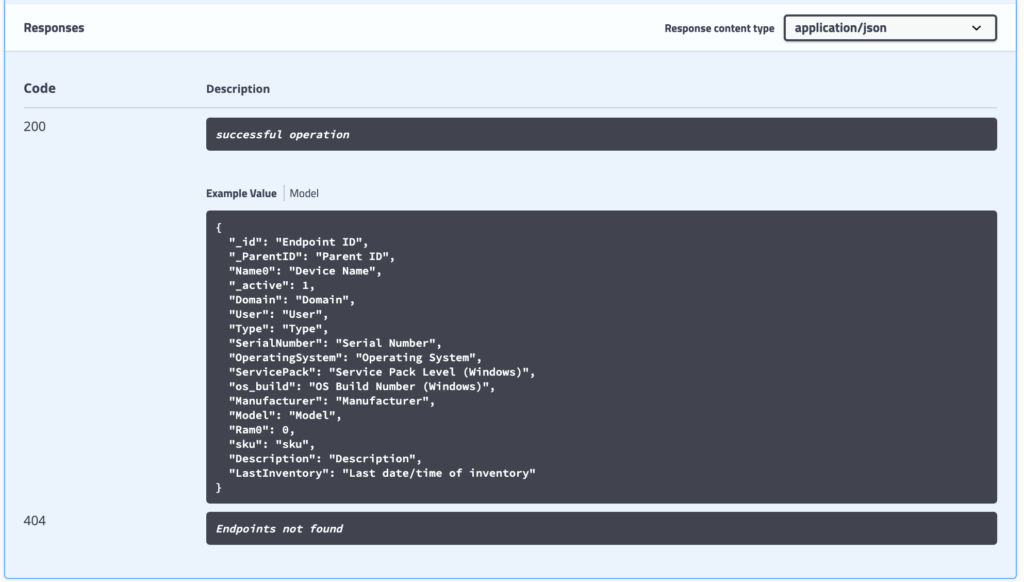
API Integration
Can you integrate with x? Can y integrate with you? If you have a tool you want to push data to, or a tool you want to pull data from, our system makes it easy to set up scheduled data transfers in an open and well-documented API environment.
Multiple deployment and hosting options
Native Windows Application
Conduct an agentless inventory from any Windows-based PC or server with a simple service account, ideal for time-sensitive projects. Wizard-based installation and configuration requires just minutes to get up and running. Full cross-platform data collection capabilities with automated insight reporting and zero technical complexity.
Virtual Appliance
For long term deployment, our virtual server appliance is distributed as an OVF image and installed on the hypervisor of your choice. Simple wizard-based installation with advanced configuration and scheduling options for distributed environments and unique network conditions, our virtual appliance provides real-time asset reporting across the enterprise.
Analytics Portal
Your asset inventory data can optionally be encrypted and securely transferred to a regionally located tier-4 datacenter where it is cleansed, categorized, matched and analyzed for advanced reporting; including installed software categorization, license assignment, hardware warranty matching, end-of-support/end-of-life status and cross-referenced with all known security vulnerabilities.